For a long time I believed something that many people in crypto still repeat almost automatically: that transparency alone fixes trust. That if every transaction is visible and every piece of data sits permanently on a distributed ledger, the problem of verification disappears. It sounded elegant. Almost poetic in a technical way. But the longer you watch how real users interact with blockchain systems, the more complicated the story becomes. Because transparency solves one problem while quietly creating another. And that tension is where the conversation around zero-knowledge infrastructure really begins.
When networks like Bitcoin first appeared, the radical idea was that nobody had to trust a bank, a government, or any central authority to verify a transaction. The system itself could prove that something happened. Every transfer recorded, every block validated, every participant able to check the ledger independently. It felt revolutionary because it replaced institutional trust with mathematical certainty. And for the early days of digital money, that design made perfect sense.
But transparency has a strange side effect once systems grow large enough. At first it empowers users. Then it exposes them.
On most public blockchains today, transactions are technically pseudonymous, but in practice the patterns become surprisingly visible. Wallet addresses move funds, interact with contracts, trade tokens, vote in governance systems, and slowly a behavioral fingerprint forms. Analytics platforms map these patterns together. Exchanges link identities to wallets. Suddenly the supposedly anonymous ledger begins to look less like a neutral record and more like a permanent activity trail. Not just for individuals, but for organizations too.
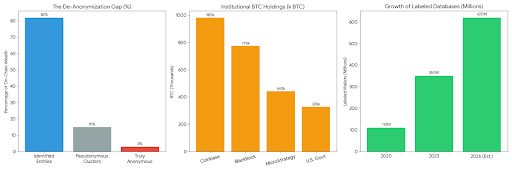
This is where the conversation starts to shift. Because the real world rarely operates in extremes. Total secrecy breaks accountability, but total transparency breaks privacy. Somewhere in the middle is where most systems actually function. And that middle ground is precisely where projects like Midnight (NIGHT) start to explore a different design philosophy.
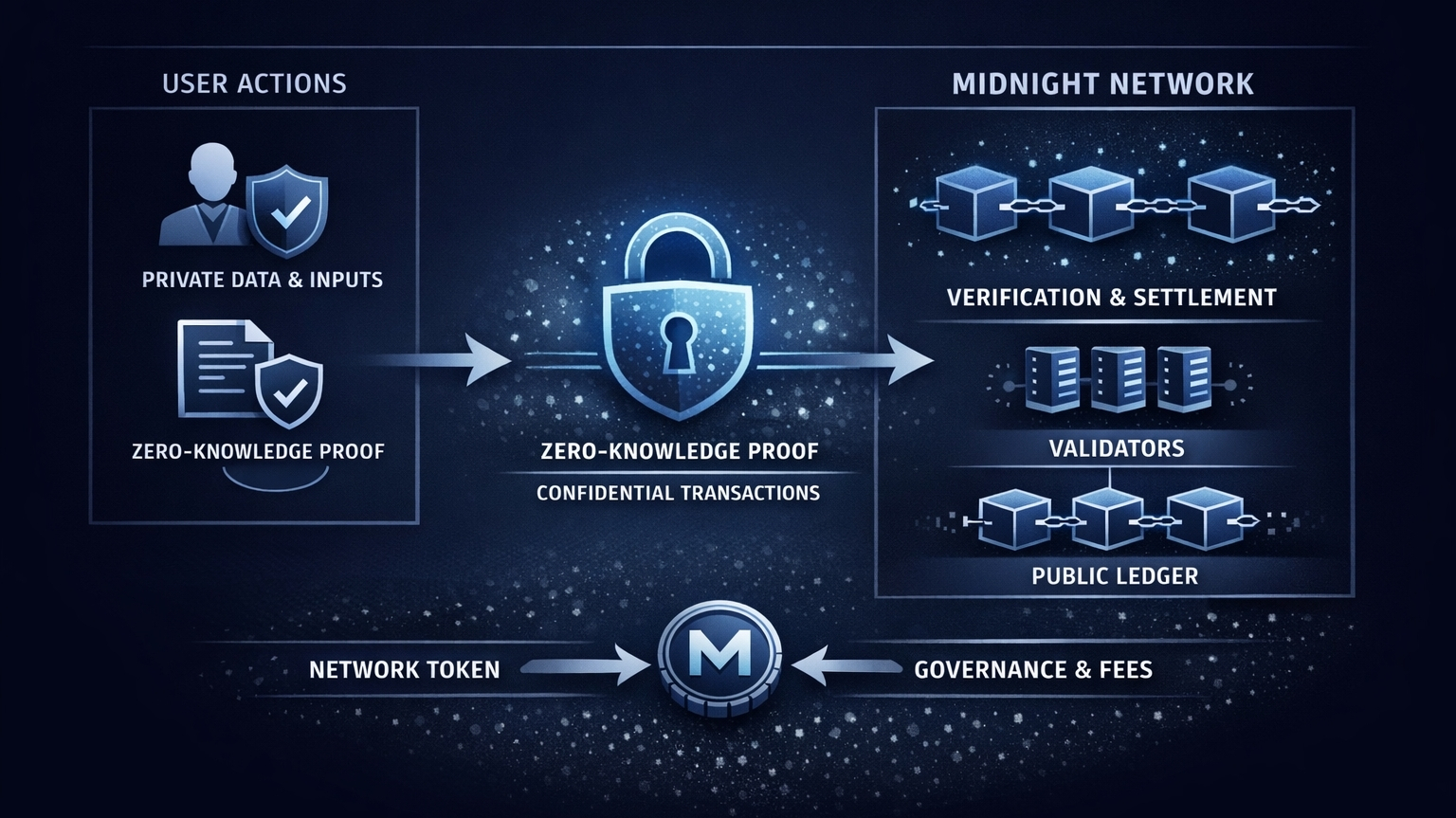
At the center of that philosophy sits a cryptographic idea that sounds almost like a paradox the first time you hear it: zero-knowledge proofs. The concept is simple in theory and complex in execution. A system allows someone to prove a statement is true without revealing the underlying information that makes it true. Imagine proving you’re eligible for something without revealing your entire identity. Imagine verifying a balance without exposing the actual amount. The network checks the condition, confirms it, and moves on. The sensitive data never becomes public.
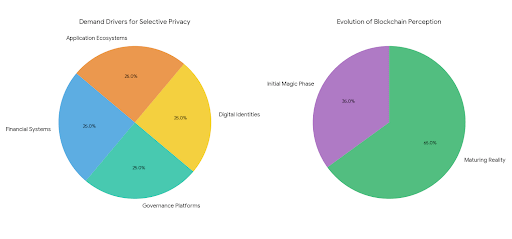
When you first encounter the idea, it almost feels like a magic trick disguised as mathematics. Yet it’s becoming increasingly important as blockchain technology matures. Because once financial systems, governance platforms, digital identities, and entire application ecosystems start operating on-chain, the demand for selective privacy becomes impossible to ignore.
Take decentralized finance as an example. On a transparent chain like Ethereum, trading strategies can be tracked in real time. Liquidity positions become visible. Arbitrage opportunities reveal themselves to anyone watching closely enough. Transparency keeps the system honest, yes, but it also introduces competitive exposure that traditional markets rarely tolerate. Traders are visible. Strategies are visible. Sometimes even intentions are visible.
Now imagine a system where transactions can still be verified by the network, but certain details remain hidden. Not completely secret, just selectively private. Enough information to maintain trust, but not enough to expose every operational detail. That subtle shift is what privacy-focused infrastructure attempts to achieve, and it’s part of the architectural logic behind Midnight (NIGHT).
The interesting thing is that this isn’t really about hiding things. That’s the misconception people often jump to. Privacy in blockchain systems isn’t the same as secrecy. It’s more about control. Who sees what, when, and why. In many ways it resembles the way information works in everyday life. You might show your ID to verify your age at a venue, but that doesn’t mean the venue needs your full identity record stored forever. The verification happens. The rest stays private.
What makes the problem tricky in decentralized systems is that verification usually requires public data. If everyone can’t see the ledger, how do they know it’s correct? That’s the puzzle zero-knowledge cryptography tries to solve. Instead of revealing the entire dataset, the system produces a proof that mathematically guarantees the result. You don’t see the underlying data, but you know the conclusion is valid.
It sounds almost philosophical when you think about it long enough. Proof without exposure. Truth without disclosure.
And perhaps that’s why privacy infrastructure has slowly become one of the more fascinating areas of blockchain development. Not because it promises dramatic price movements or flashy token narratives, but because it quietly addresses a structural limitation that early blockchains never fully resolved. The early networks optimized for transparency because transparency solved the immediate trust problem. The next generation is experimenting with something more nuanced.
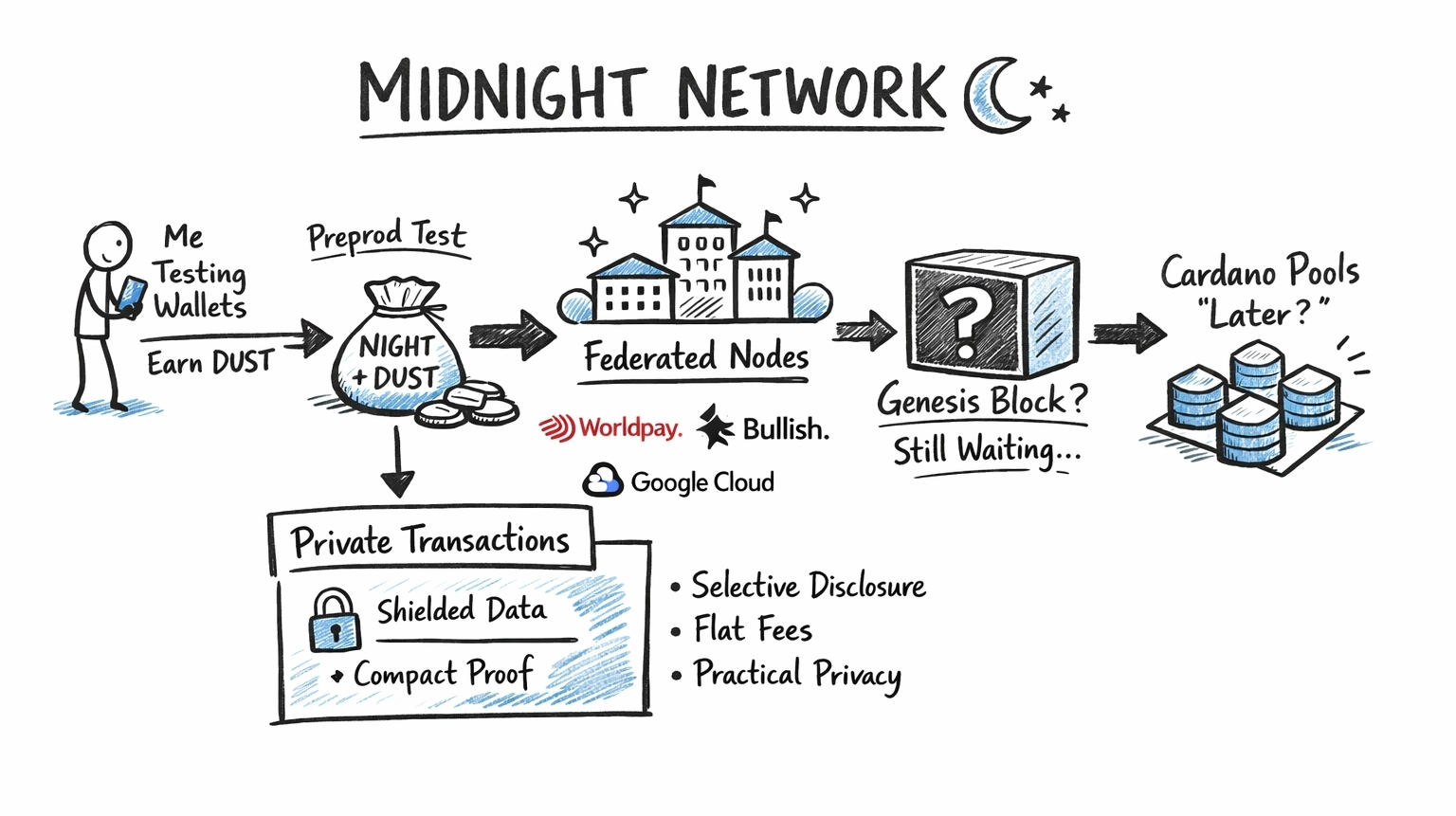
Projects like Midnight (NIGHT) attempt to build that nuance directly into the infrastructure layer. The goal isn’t to replace public blockchains but to expand what they can do. A system where applications can choose when to reveal data and when to keep it private. Where users maintain ownership over their information while still interacting with decentralized networks. Verification continues, but exposure becomes optional.

Of course, ideas like this tend to attract attention quickly in the crypto industry, and attention often arrives faster than actual adoption. That’s another pattern worth acknowledging. The market loves narratives. Zero-knowledge proofs, privacy chains, modular blockchains every few years a new infrastructure story captures collective imagination. Sometimes the technology delivers exactly what it promised. Other times the excitement fades before real usage appears.
It’s easy to measure things like wallet numbers or token holders. Those metrics look impressive on dashboards and investor presentations. But they can also be misleading. Wallet creation is simple. Activity is harder. The real indicator of a healthy ecosystem is the number of applications people actually use and the consistency of that usage over time.
Infrastructure projects face a unique challenge in this regard because their success depends heavily on developers. Builders need tools, documentation, frameworks, and time. Especially with something as technically demanding as zero-knowledge cryptography. Writing smart contracts is already complex. Writing contracts that interact with cryptographic proofs adds another layer of difficulty.

That complexity can slow adoption, at least initially. But it can also create strong foundations once the tooling improves. Many technologies follow this pattern. Early development feels slow and experimental, then suddenly a wave of practical applications appears once the barriers to entry drop.
In some ways the conversation around privacy infrastructure feels similar to earlier debates about scalability. At first it was mostly theoretical. Researchers discussing possibilities, developers experimenting with prototypes, communities arguing about trade-offs. Eventually the tools improved and entire ecosystems formed around scaling solutions. Privacy could follow a similar path.
Still, it’s important not to romanticize the technology too much. Every infrastructure experiment carries risks. Cryptographic systems must be implemented correctly, and mistakes can be catastrophic. Performance optimization remains a constant challenge. Generating and verifying proofs requires computational work, and networks must handle that workload efficiently if they want to support large numbers of users.
There’s also the simple question of timing. Markets move quickly. Infrastructure evolves slowly. Sometimes the two rhythms clash.
Yet despite those uncertainties, the broader direction of blockchain development seems to be moving toward more sophisticated data management models. The first generation proved that decentralized verification works. The second generation is exploring how that verification can coexist with privacy, compliance, and real-world constraints.
And maybe that’s the quiet evolution happening underneath the surface of the industry right now. Not a dramatic revolution, not a sudden shift, but a gradual recognition that transparency and privacy are not opposites. They’re variables. Systems can adjust them depending on context.
Projects like Midnight (NIGHT) sit somewhere in that exploration, experimenting with what happens when verification and confidentiality are designed together instead of treated as separate problems. Whether they succeed will depend on something surprisingly simple: whether developers find genuine reasons to build applications that require this balance.
Because technology alone rarely decides the future of an ecosystem. Usage does.
And sometimes I wonder if the most important infrastructure in the next phase of Web3 won’t be the loudest or most visible networks, but the quiet layers working in the background systems proving things are true while revealing almost nothing at all.
@MidnightNetwork #night $NIGHT
