Here Is How They’re Trying to Make That True and Where It Gets Complicated.
the core promise of an omni-chain attestation protocol is that a verified claim doesn’t stop being verified when it crosses a chain boundary. that sounds obvious until you try to build it.
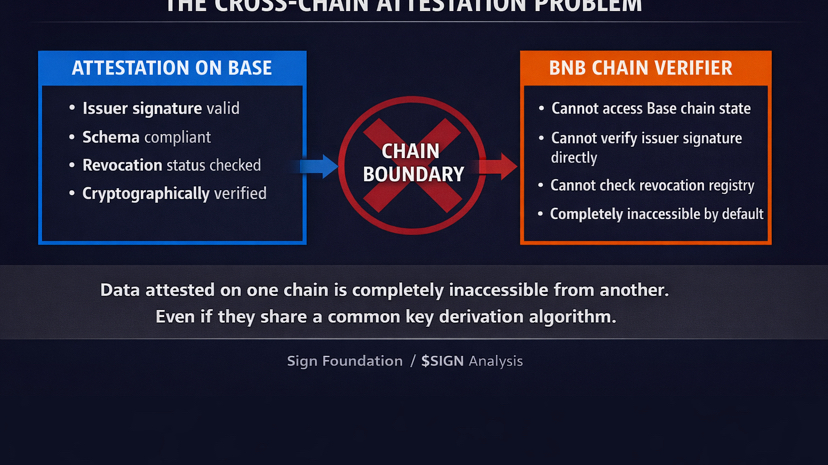
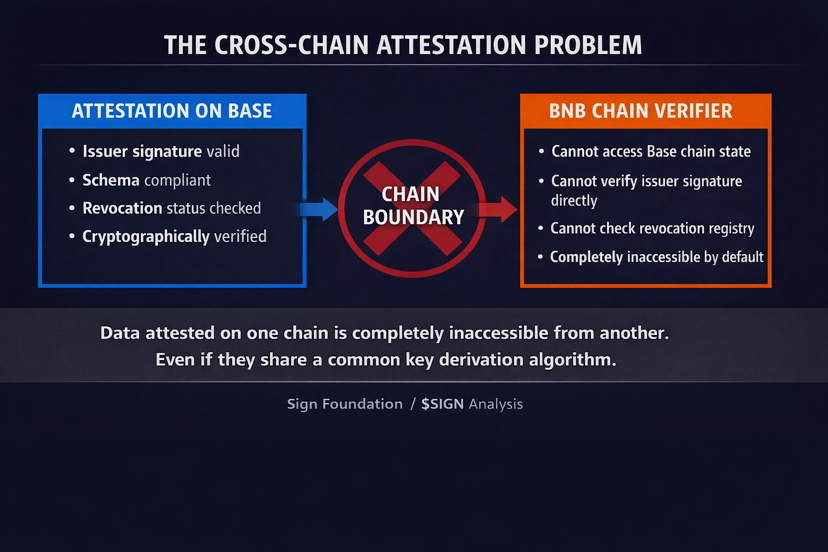
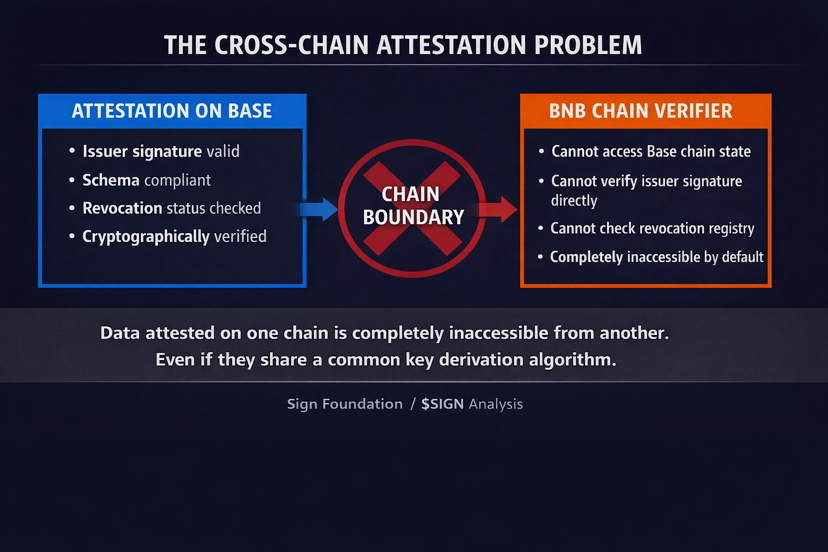
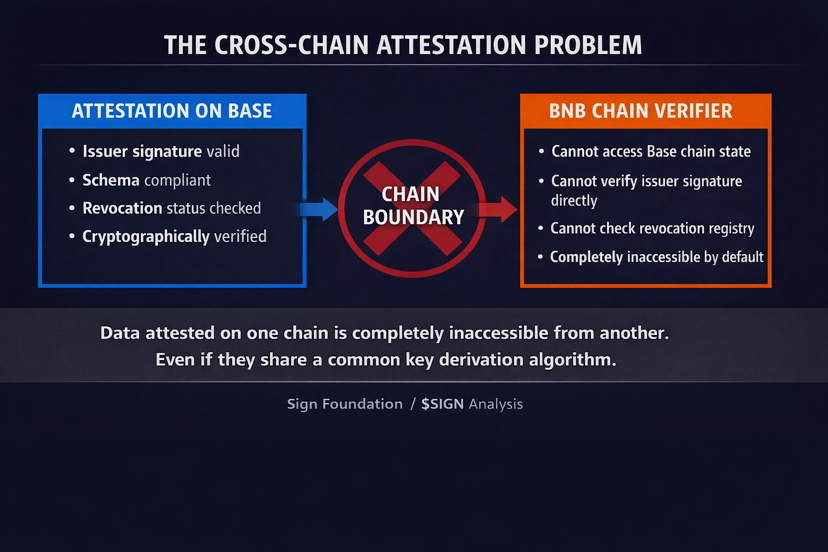
@SignOfficial states this directly in the cross-chain attestation documentation. data that’s digitally signed and attested on Base should be just as valid on BNB Chain. the problem is that blockchains don’t talk to each other natively. an attestation recorded on one chain is completely inaccessible from another chain even if they share a common key derivation algorithm.
that’s not a small engineering problem. it’s the fundamental fragmentation issue that makes cross-chain anything difficult. and for a protocol positioning itself as sovereign infrastructure for the Middle East, where different government systems may run on different chains, it’s the problem that determines whether the cross-border verification thesis is real or theoretical.
$SIGN #SignDigitalSovereignInfra
the existing cross-chain solutions didn’t work for what Sign needed.
the documentation is specific about this. Chainlink CCIP and LayerZero are mature solutions. @SignOfficial evaluated them and found they didn’t satisfy the flexibility the protocol requires. the specific example given is pulling and validating data from atypical blockchains like Arweave. existing bridges are built for EVM-to-EVM transfers. Sign’s attestation use cases don’t stay neatly inside that boundary.
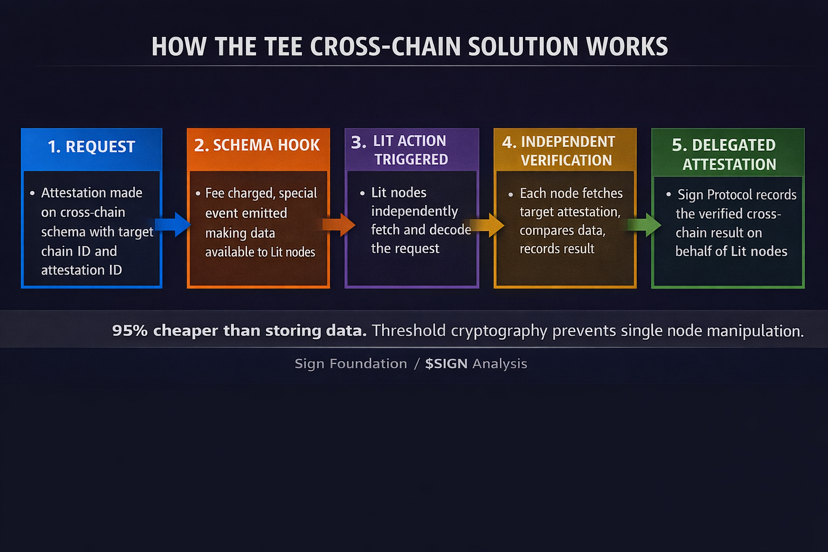
so they partnered with Lit Protocol and built a TEE-based cross-chain verification solution instead.
a TEE is a Trusted Execution Environment. a secure isolated part of a processor that runs operations in a way that’s protected from the rest of the system, including the main operating system. the isolation means that even if the surrounding environment is compromised, the computation inside the TEE remains trustworthy. Intel SGX, ARM TrustZone, AMD’s architecture powering Lit Protocol’s decentralized hardware offering are all examples.
the way Sign uses it is specific. a cross-chain verification request triggers Lit nodes to independently fetch the target attestation on the target chain, compare it against the data being verified, and return a signed result using threshold cryptography. at least two thirds of the entire Lit network must sign the result before it’s considered valid. that threshold signature is what makes the cross-chain verification trustworthy.
#SignDigitalSovereignInfra $SIGN

here is where the tension appears.
the TEE model introduces a new trust assumption that isn’t present in a single-chain attestation. when you verify an attestation on the same chain it was issued, the trust chain is: issuer signature, schema compliance, revocation status. all of it is verifiable directly from chain state. no external party required.
when you verify an attestation cross-chain using the TEE model, the trust chain becomes: issuer signature, schema compliance, revocation status, plus the integrity of the TEE hardware, plus the honest behavior of at least two thirds of the Lit network nodes, plus the correct execution of the Lit Action that fetches and compares the data.
that’s a longer trust chain. each additional link is an additional assumption.
the threshold cryptography requirement, two thirds of the Lit network, is designed to make the cross-chain result resistant to individual node compromise. that’s the right design choice. it means a single malicious node cannot forge a cross-chain verification result.
what it doesn’t fully address is the question of what happens if the Lit network itself has a systemic issue. the cross-chain attestation result is signed by Lit nodes, not by the original issuer. a verifier accepting that result is trusting the Lit network’s integrity as a proxy for the original attestation’s validity.
for a developer building a DeFi application that’s probably an acceptable trust tradeoff. for a government using cross-chain attestations to verify sovereign credentials across border infrastructure the question of whether a decentralized hardware network constitutes sufficient trust for national-level verification is genuinely open.
what @SignOfficial gets right is recognizing that the problem existed and building a specific solution rather than pretending existing bridges were sufficient. the 95% gas efficiency improvement from encoding data in extraData instead of storing it is a real engineering optimization. the threshold cryptography requirement is a real security design.
the Middle East cross-border use case is exactly where this matters most. a UAE attestation being verified by a Saudi system may run on different chains. the cross-chain attestation mechanism is the technical bridge that makes that possible.
honestly the more i read through this the more i think the TEE approach is the right technical direction and the trust assumption question is the right thing to be asking about it. not because the design is wrong. because the contexts where Sign is deploying this infrastructure, national governments, sovereign institutions, cross-border financial systems, are contexts where every trust assumption needs to be explicit and understood before deployment.
a TEE-based cross-chain verification solution that makes omni-chain attestations practically possible, or a trust chain extension that introduces new assumptions that sovereign deployments need to explicitly evaluate before relying on it?