When people talk about digital identity in crypto the conversation usually starts with control. Ownership of data privacy self sovereignty. These are important ideas but they often stay at the surface level. What gets less attention is how identity actually behaves once it enters real products.
Because in practice users do not wake up wanting to manage identity. They want to log in transact access services and move between applications without friction. Identity only becomes valuable when it stops being visible as a task and starts functioning as a seamless layer beneath everything else.
That distinction is where many identity systems struggle.
Early designs often treated identity as a standalone feature. Wallet connections credential dashboards verification steps. Each interaction added a layer of complexity. Even if the system was technically decentralized the user experience remained fragmented. And when friction increases adoption slows regardless of how strong the underlying idea is.
This is why the conversation around #SignDigitalSovereignInfra feels slightly different. It shifts focus from identity as a feature to identity as infrastructure. The goal is not just to give users control but to make that control usable without requiring constant interaction or awareness.
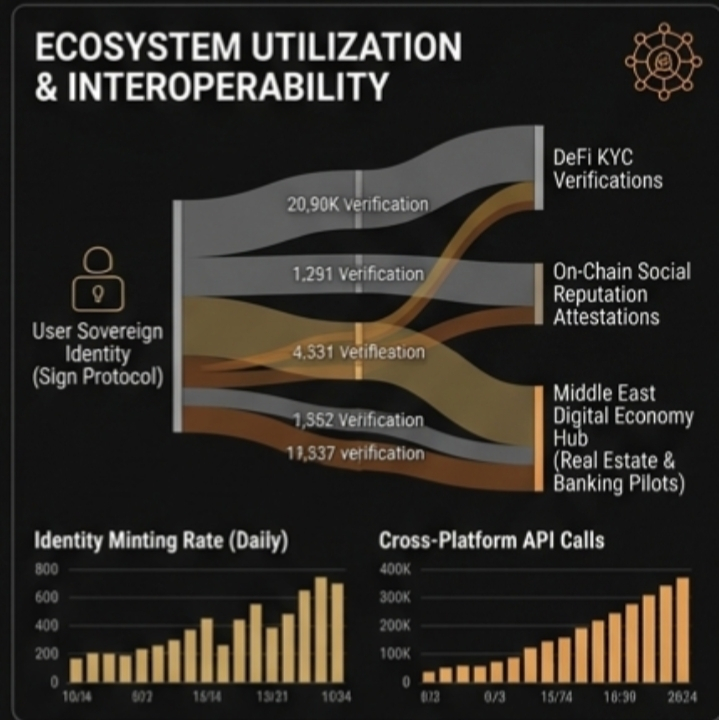
In this model identity behaves more like a background process. Users generate verifiable credentials once and those credentials can be reused across multiple applications. Instead of repeatedly submitting data or trusting each platform individually users carry proof with them. Applications request only what they need and verification happens without exposing the full dataset.
The key here is abstraction.
If the system works users should not need to think about cryptographic proofs validators or data structures. They should experience faster onboarding fewer repeated steps and greater continuity between platforms. Developers on the other hand get access to a reliable identity layer that reduces the need to build custom verification systems from scratch.
That is where infrastructure begins to show its value. Not in visibility but in removal of friction.
The integration of $EDGE and $UAI adds another layer to this dynamic. AI systems can process and validate identity related data off chain handling complexity before it reaches the user. Sign then anchors those results in a verifiable user owned framework. This separation between processing and verification allows the system to scale without compromising ownership.
It also opens up new types of interactions.
For example AI agents could act on behalf of users in certain contexts verifying eligibility reputation or credentials in real time. But instead of holding identity themselves they rely on a system where the user remains the source of truth. This creates a balance between automation and control something that becomes increasingly important as AI systems take on more responsibility.
From a network perspective this design introduces a different kind of demand.
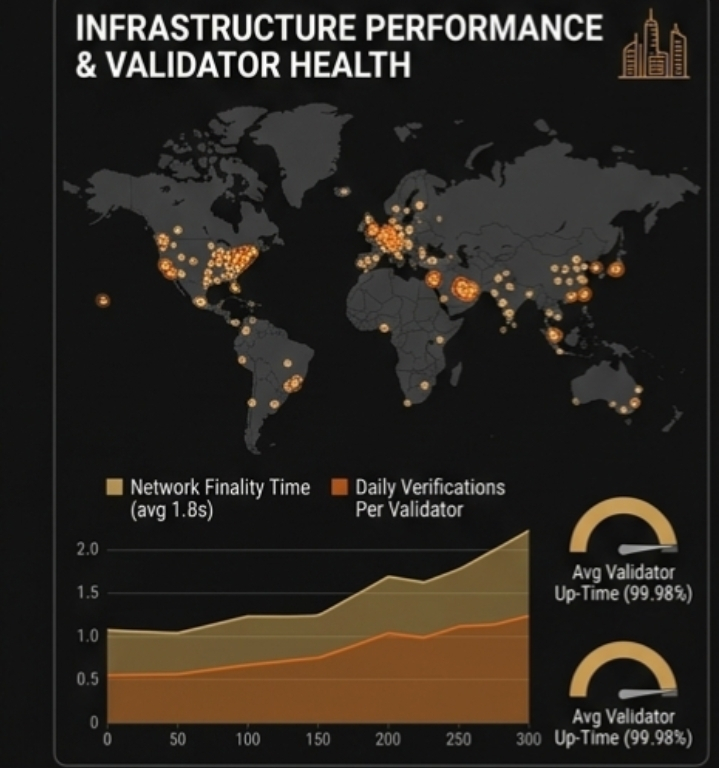
Instead of users interacting directly with identity as a product identity becomes embedded in every interaction that requires trust. Logging into applications accessing financial services participating in governance verifying credentials. Each of these actions generates activity within the network even if the user is not explicitly aware of it.
That is what makes infrastructure powerful. It scales with usage of the ecosystem not with attention to itself.
But this also makes evaluation more complex.
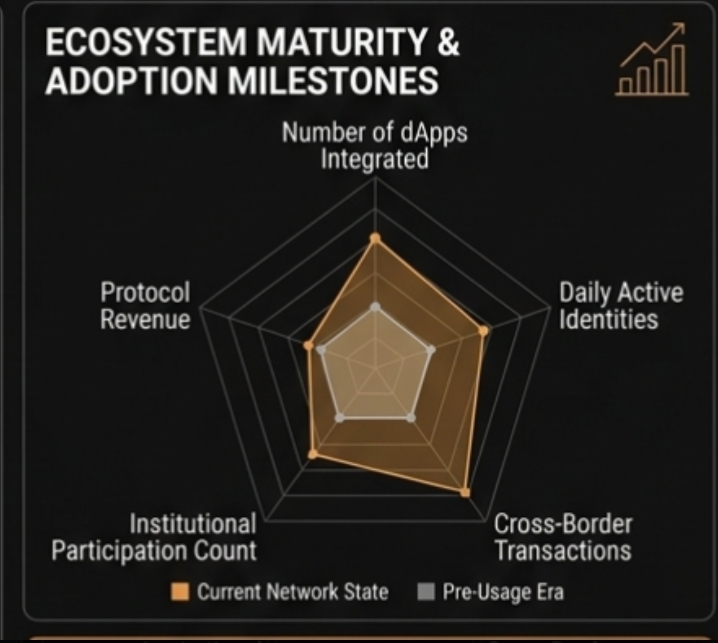
You cannot measure success purely by how many people are talking about identity. You have to look at how often it is being used implicitly. Are developers integrating it into onboarding flows. Are applications reducing friction because of it. Are users moving between platforms more easily without repeated verification.
These signals are harder to track but they are more meaningful.
The risk as always is that the system remains technically sound but underutilized. If developers do not embed identity into core product flows it stays optional. And optional features rarely drive sustained engagement. On the other hand if identity becomes a default layer across applications it starts compounding in value over time.
This is where timing and ecosystem alignment matter.
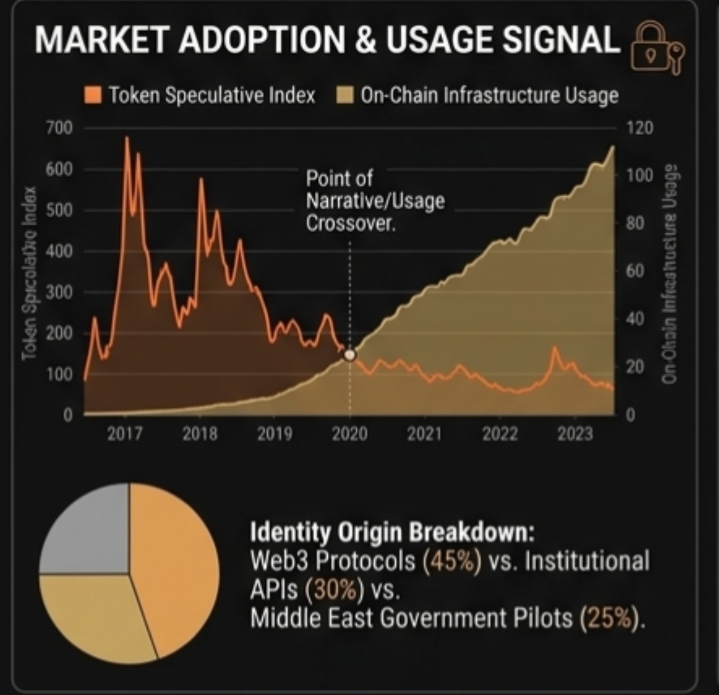
In regions investing heavily in digital infrastructure particularly across the Middle East the need for interoperable and verifiable identity systems is growing. Not just for individuals but for businesses institutions and cross sector coordination. A system like Sign has the potential to operate as a shared layer across these environments reducing fragmentation and increasing trust between participants.
That shifts identity from a niche crypto primitive to a broader economic enabler.
Still the same principle applies. It only works if it is used.
So the real question is not whether digital sovereignty is important. It is whether it can integrate so smoothly into products that users stop noticing it altogether. Because that is when infrastructure becomes real. Not when people talk about it but when they rely on it without thinking.
And in systems like this the strongest signal is always the simplest one. Do people keep using it after the narrative fades.