I kept running into this inside Sign’s TokenTable while trying to map eligibility flows across a Gulf-based distribution pilot. Not the token logic itself. The identity layer. Specifically, who gets recognized as “valid” when multiple issuers, jurisdictions, and attestations start colliding in the same table. Sign looks clean from the outside, but once you’re inside the attestation graph, admission stops feeling neutral. Identity stops being a record and becomes a filter.
The friction shows up the moment you try to reuse an attestation across contexts. A KYC badge issued for a fintech sandbox in the UAE does not behave the same when referenced inside a Saudi distribution workflow, even if both technically resolve on-chain. Sign lets you anchor both, but TokenTable forces a decision: which issuer carries weight here? That sounds like governance. It’s actually routing.
One mechanical example. We tested a scenario where two issuers provided equivalent credentials for the same participant, one from a regional bank and another from a local regulator-backed platform. Both were valid. Both cryptographically verifiable. But when TokenTable evaluated eligibility, only one path propagated cleanly through the allocation logic. The other stalled, not rejected outright, just not prioritized. Same identity. Different route. That changed who received allocation in the first pass.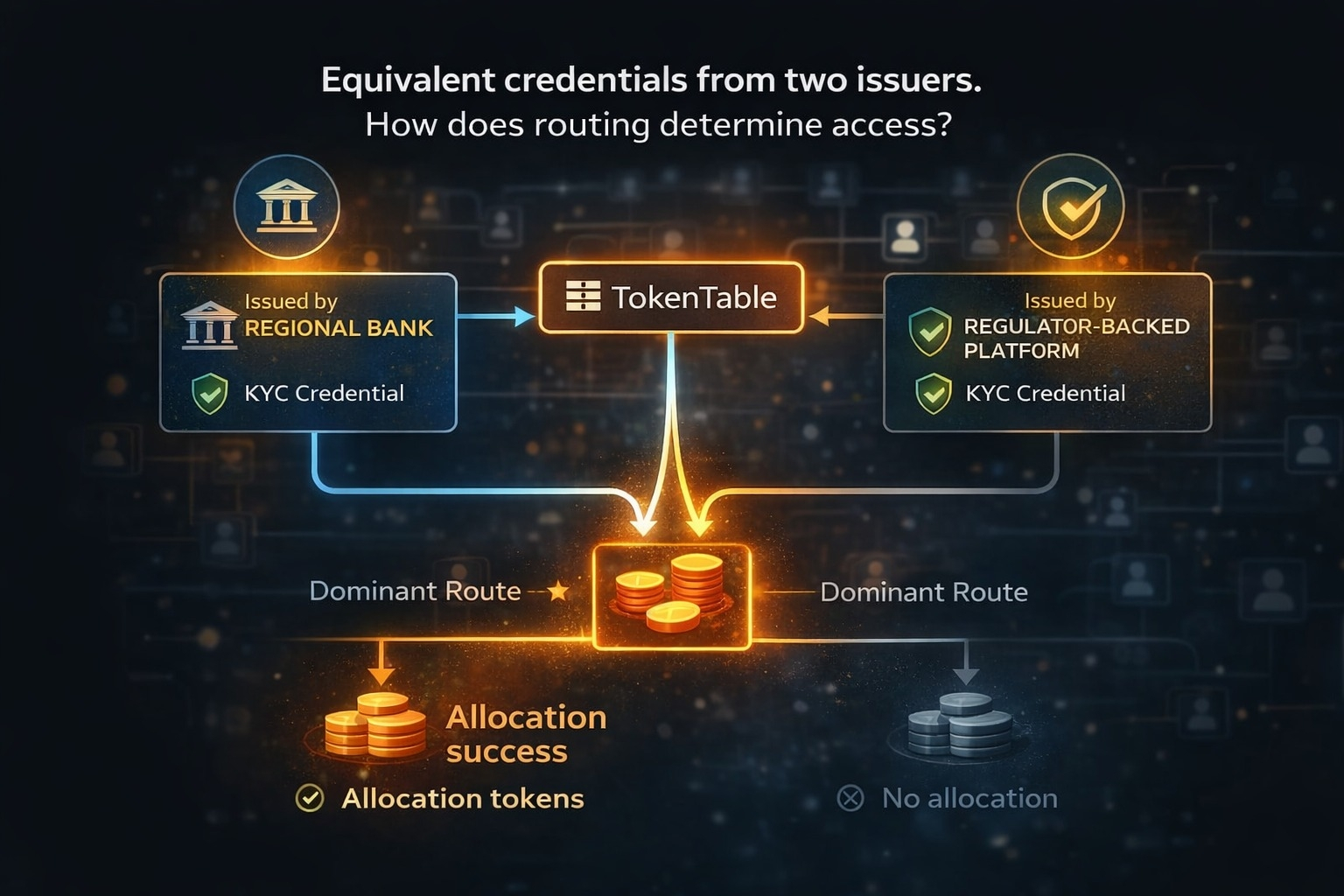
So the risk that got reduced is obvious: you avoid low-quality or spoofed attestations flooding the system. But the failure mode that becomes harder is more subtle. It becomes difficult to detect when a legitimate identity is being underweighted simply because its issuer sits outside the dominant routing path. Nothing breaks loudly. It just… doesn’t include.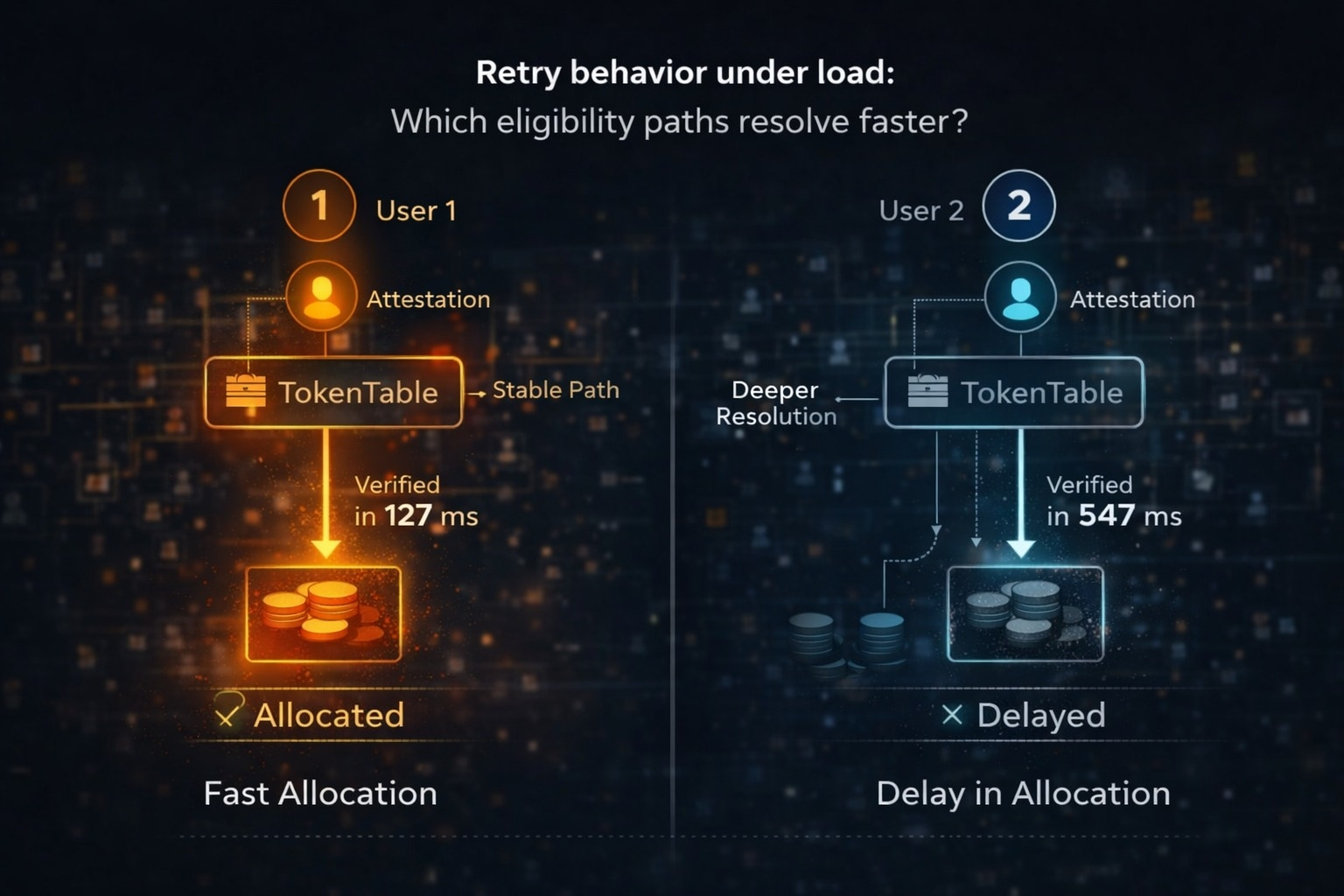
And the cost shows up as redundancy. Teams start collecting multiple attestations for the same user, not because they need stronger proof, but because they need compatibility with whatever routing layer TokenTable implicitly favors. Identity inflation. You feel it in onboarding time.
Second example. Retry behavior under load. When eligibility queries spike, especially during allocation windows, the system doesn’t just slow down uniformly. Some attestations resolve faster because their issuers are already cached or prioritized within the evaluation graph. Others require deeper resolution, more hops, more checks. In practice, this means two identical users can experience different inclusion timing based purely on how “close” their issuer is to the active routing layer.
What changed in workflow is small but persistent. You stop asking “is this identity valid?” and start asking “will this identity resolve fast enough when it matters?” That’s a different question.
There’s a tradeoff here that doesn’t sit comfortably. By tightening which attestations flow smoothly, Sign reduces noise and coordination overhead. But it also creates a quiet gradient of privilege based on issuer proximity. Not intentional, maybe. But operationally real.
I’m not fully convinced this stabilizes at scale. It might. Or it might just formalize a new kind of gatekeeping that looks decentralized on paper.
If this system were to extend into broader Middle East economic workflows, say subsidy distribution, licensing, or cross-border workforce verification, this routing bias would not stay abstract. It would show up as repeated behavior. Certain identities consistently clearing faster. Certain issuers becoming default bridges. Others fading out, even if technically sound. You’d start seeing patterns like:
• Teams pre-selecting issuers before onboarding users
• Participants re-attesting through “accepted” channels just to avoid delays
• Allocation cycles clustering around specific identity providers
And if adoption doesn’t happen evenly, the system doesn’t fail outright. It fragments. Different sectors or jurisdictions would anchor to different issuer clusters, and cross-context portability, which Sign is supposed to enable, becomes conditional again.
The token only starts to make sense once you feel this coordination pressure. $SIGN isn’t just sitting there for incentives. It quietly underwrites which interactions get prioritized, how issuers align, and how verification costs are absorbed. Not in price terms. In behavior. Who stakes, who validates, who becomes part of the fast path. You can almost treat it as a gravity layer for identity routing.
There are small signals already. Developers defaulting to a narrow set of issuers when building flows. Repeated integrations with the same attestation providers. Less experimentation than you’d expect in an open system. That could be early-stage caution. Or it could be the beginning of convergence around a few “safe” identity routes. Two open tests I keep coming back to:
If you onboard a new issuer with strong credentials but no existing routing weight, does it naturally gain usage, or does it stay peripheral?
If you deliberately route through a less common attestation path, do you see consistent delays or exclusions during peak allocation?
And one more, harder to simulate without scale: when multiple jurisdictions start interacting through the same TokenTable, does one identity standard quietly dominate?
What I’m watching is not throughput or transaction count. It’s repetition. Which identities keep showing up in successful allocations, and which ones slowly disappear from the graph even though they never technically failed.
If Sign’s identity layer is going to act as infrastructure in these systems, the real question isn’t whether identities can be verified.
It’s whether they can move without friction across contexts that don’t share the same default trust paths. I’m not sure yet that they can.
@SignOfficial #signdigitalsovereigninfra $SIGN
